Gartner Hype Cycle 2021: Identity and Access Management Technologies
As per Gartner,
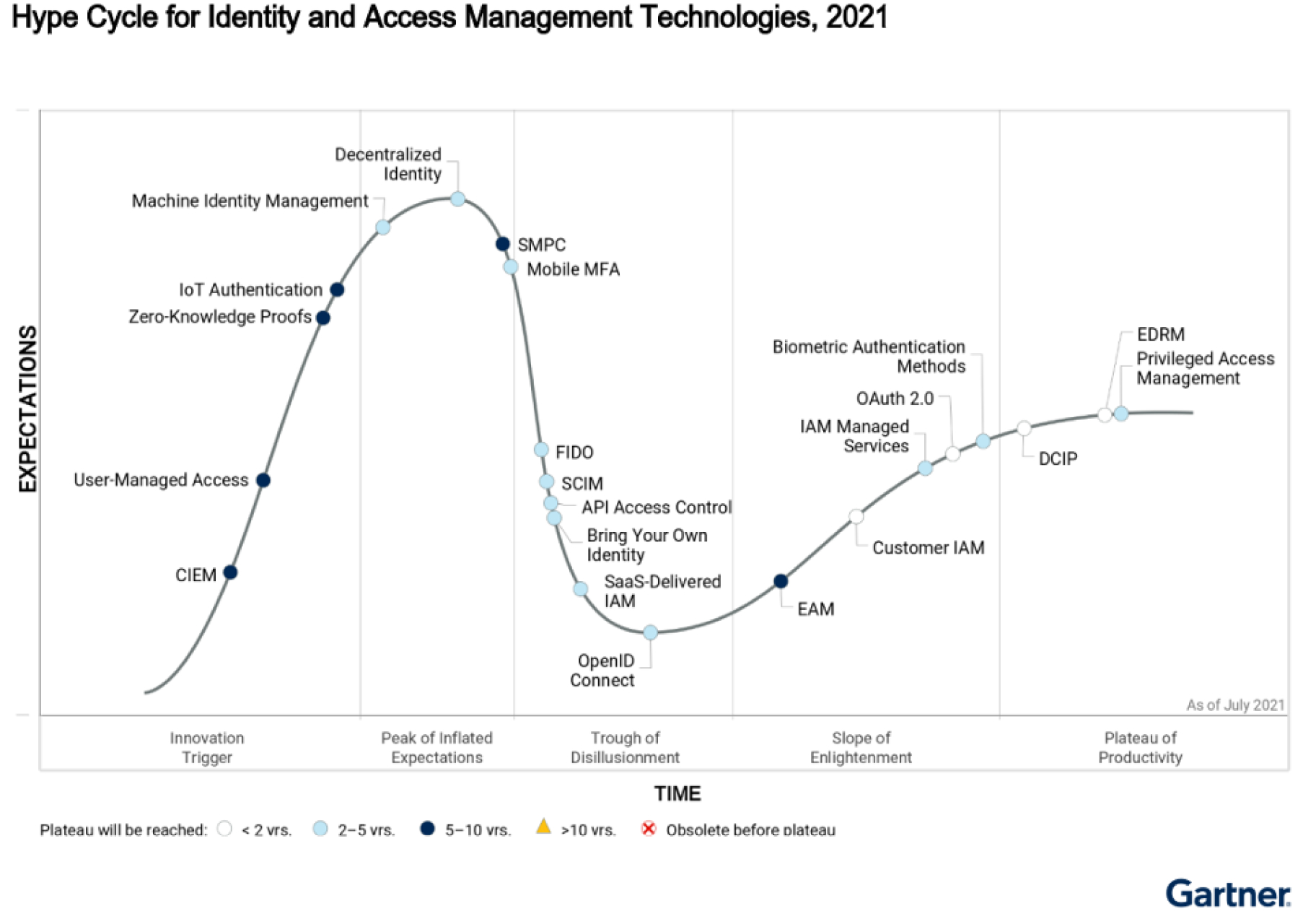
“Security and risk management leaders can use this research to find technologies to combat complex identity-based attacks. Machine identity management and decentralized identity dominate the Peak of Inflated Expectations, while FIDO and SaaS-delivered IAM are already in the Trough of Disillusionment…”.
Let InfoCert, a Leader for eSignature Software, support you in the digitalization of Business Approval processes in a secure and fast way
The IDC MarketScape evaluates 15 e-signature solution providers on the basis of their capabilities and strategies related to their offerings. InfoCert has been placed in the “Leaders Category“.
Click on the button below to discover the report at gartner.com
The Hype Cycle
IAM is a security, risk management and business discipline. It encompasses practices, processes and technologies that manage the identities and entitlements of people, services and things, and the relationships between, and trust associated with, them. Effective IAM technologies equip IAM leaders and their teams to provide the right access for the right reasons. They thereby enable the right interactions at the right time — and with the right user experience (UX) — to help drive desired business outcomes and digital experience goals.
The dramatic rise of remote working, combined with high-profile identity-based attacks, has resulted in an increase in deployments of multifactor authentication (MFA). While many of those deployments have used well-established MFA factors, there has also been increased focus on streamlining the UX (from anywhere) with strong, but lower-friction, user authentication and access management (AM). This has resulted in standards-based protocols like OpenID Connect (OIDC), Fast IDentity Online 2 (FIDO2) and System for Cross-Domain Identity Management (SCIM) leaping forward in adoption and appearing on more client roadmaps. These significant developments, reflected in the Hype Cycle, demonstrate that standards-focused AM tools continue to grow in importance, and support a consistent approach to diverse application architecture and user roles.
Decentralized identity and secure multiparty computation, though still at the Peak of Inflated Expectations, have moved forward. Their progress has been driven partly by the increased need for privacy preservation, as well as by the requirement for high-assurance digital identities. Secure, high-assurance, remote access to government services, banking services and other critical or high-risk interactions is now mandatory, and legacy strategies have proven insufficient, due to a lack of consumer control and the risk of fraud.
Privileged access management (PAM) adoption has moved further along the Plateau of Productivity. It is now a basic requirement, as many of the most damaging attacks of the past year have involved attacks on human and machine privileged accounts. Machine identity management has advanced to the Peak of Inflated Expectations.
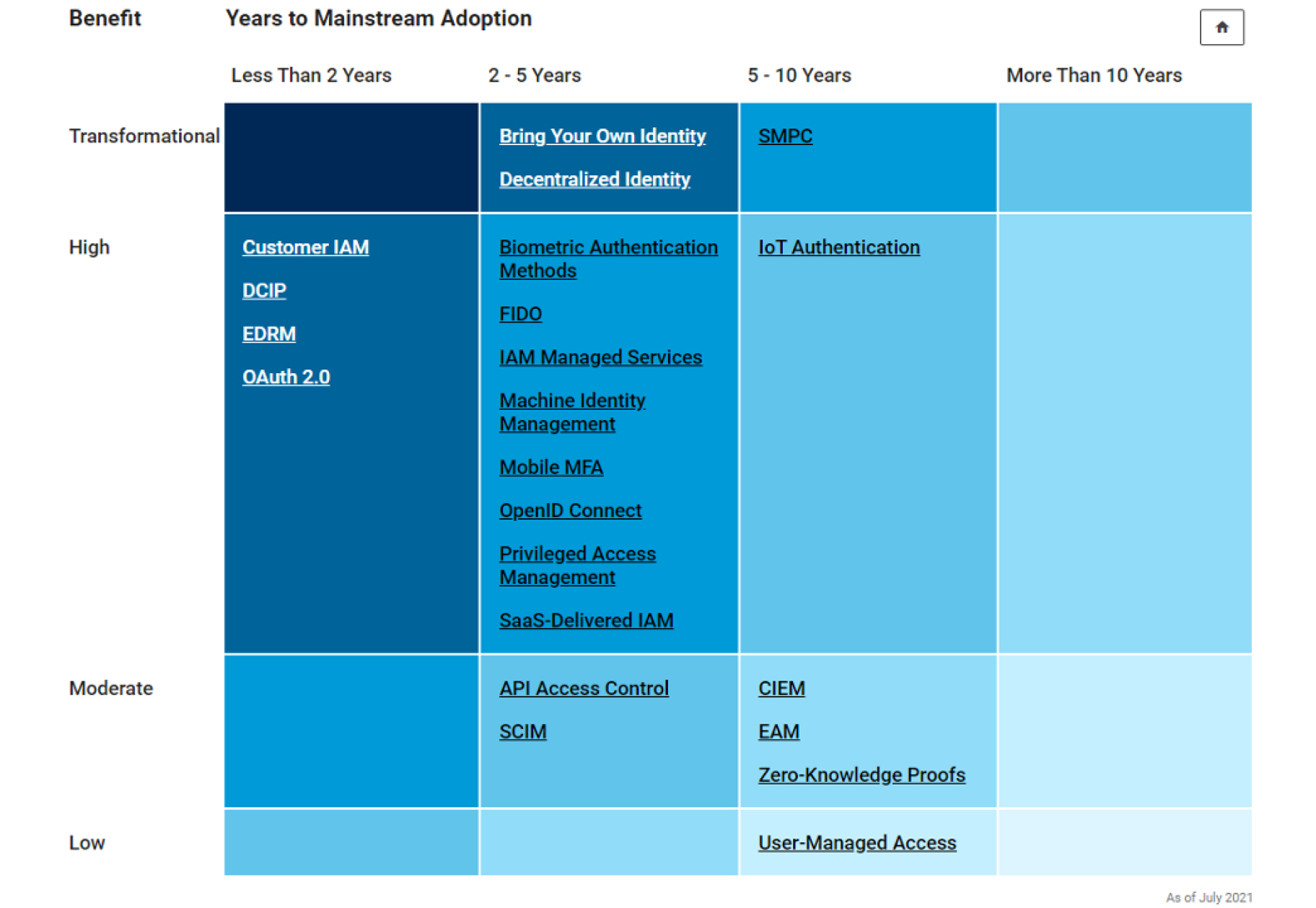
The Priority Matrix illustrates the technologies mapped to the time frame by which they are expected to mature into mainstream adoption and deliver benefits, and the level and depth of benefits that can be expected from them.
Let InfoCert, a Vendor recognized by Gartner, introduce your Organization to the benefits and the emerging technologies such as Decentralized Identity.
Gartner, Hype Cycle for Identity and Access Management Technologies, 2021 , 27 July 2021, Tricia Phillips.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose. GARTNER and Hype Cycle are registered trademarks and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved. This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from InfoCert S.P.A


